Fake domains and why they’re bad
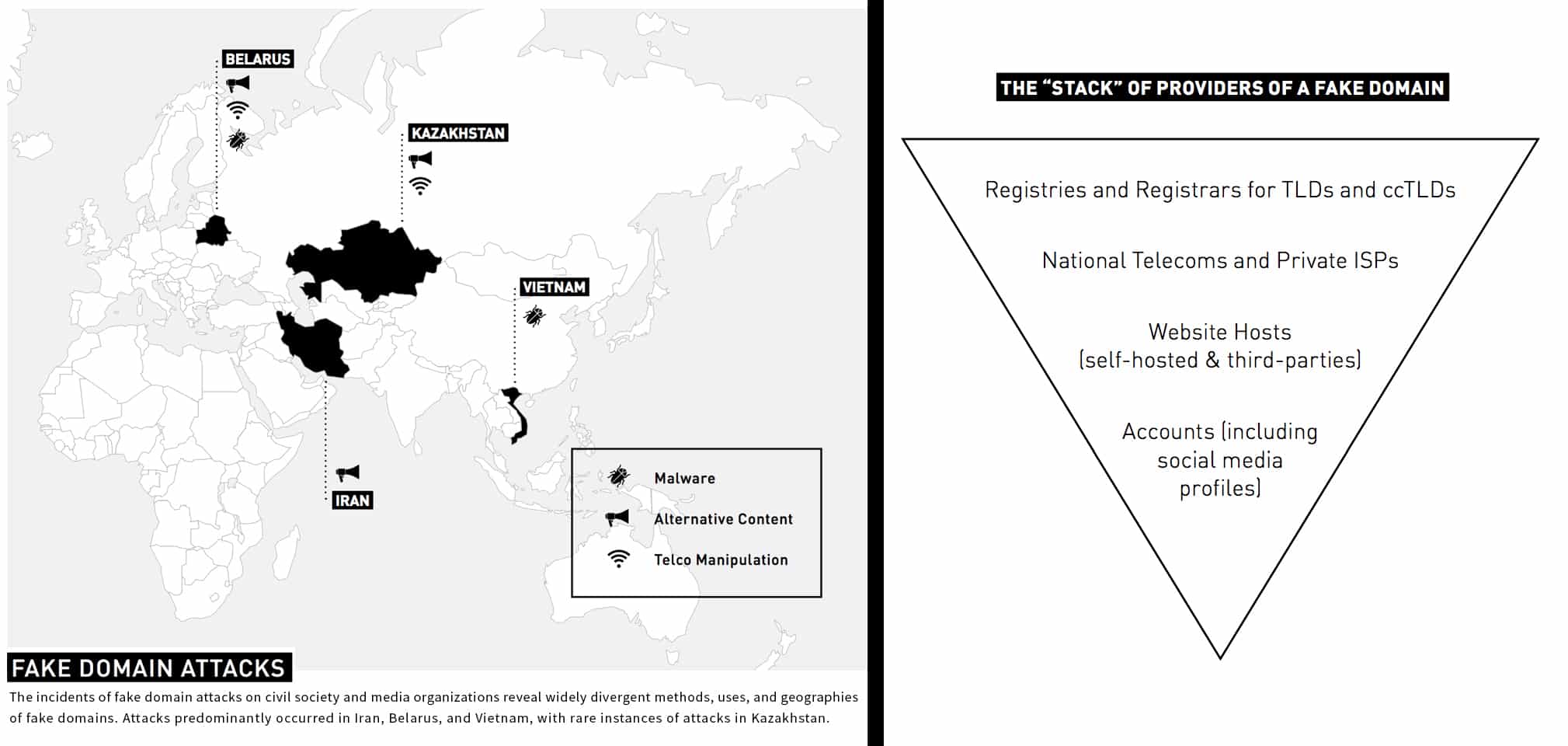
Civil society organizations and independent media are the targets of a variety of sophisticated attacks to compromise their websites’ and users’ security. One common form of attack is known as “fake domains,” which refers to situations where an adversary creates a fake website or social media profile that looks similar or identical to the legitimate one, with the intent to:
- trick users into sharing their private information, such as banking credentials or other account passwords;
- draw readership from the original website and display alternative content;
- create confusion among a targeted community; or
- serve malware to compromise the original site’s target audience.
The effect of such imitation can be extremely harmful to consumers of media and the supporters of civil society organizations, particularly during elections, critical social demonstrations, and other important political events. Attackers have successfully drawn a significant amount of both domestic and international traffic away from victimized domains, limiting access to information or spreading misinformation, inhibiting people’s ability to organize, and undermining individuals’ security.
What we did and found
In 2013, Access Now released “One of These Things Is Not Like the Other — A Report on Fake Domain Attacks” analyzing the use of fake domains to target civil society around the world and outlining mitigation strategies for defending against such attacks.
Since then, we have continued to observe an increase in the use of fake domain attacks targeting at-risk users on a global scale, and Access Now’s Digital Security Helpline regularly assists civil society, human rights defenders, and independent media in protecting against and responding to these attacks.
Contact Helpline
If you are a victim or know of any fake domain attack affecting civil society organizations, please contact us at [email protected]. Our Digital Security Helpline is available 24/7/365 to assist members of civil society in handling fake domain attacks, and documenting attacks can help us to better defend against them in the future.